Home Care Data Security & Privacy: Protecting Patient Information
Home care agencies manage sensitive patient data across mobile devices, cloud platforms, and multiple locations. This guide covers HIPAA data security requirements, cybersecurity threats, and practical protection strategies with interactive assessment tools. For a step-by-step compliance action plan, see our HIPAA compliance checklist.
Published April 3, 2026 · 19 min read
The Threat Landscape for Home Care
Healthcare is the most targeted industry for cyberattacks, and home care agencies are particularly vulnerable. According to the HHS Office for Civil Rights (OCR), healthcare data breaches affected over 167 million individuals in 2023 alone, a record year. Smaller healthcare organizations like home care agencies are disproportionately targeted because they often have weaker security postures than hospitals.
Home care cybersecurity faces unique challenges. Caregivers access patient data from mobile devices in client homes, often over unsecured Wi-Fi networks. Staff turnover means constant provisioning and de-provisioning of access credentials. The move to cloud-based electronic health records has expanded the attack surface. And the value of patient data protection goes beyond compliance; a single healthcare record sells for $250-$1,000 on the dark web, compared to $5-$10 for a credit card number. Our HIPAA technology compliance guide details the technical safeguards your software must have.
The FBI's Internet Crime Complaint Center (IC3) reported that healthcare ransomware attacks increased 278% between 2020 and 2025. The average cost of a healthcare data breach reached $10.93 million in 2025 (IBM/Ponemon), making it the most expensive industry for breaches for the 15th consecutive year.

Protecting patient data requires a combination of technology, training, and policies that work together across every device and location.
Common Attack Vectors in Home Care
Understanding how attackers target home care agencies is the first step toward building effective defenses for patient data protection.
Phishing & Social Engineering
90%+Fraudulent emails, texts, or calls that trick staff into revealing credentials or clicking malicious links. The most common entry point for healthcare breaches.
Ransomware
278% increaseMalware that encrypts patient data and demands payment. Can shut down operations for days or weeks. Average ransom demand for healthcare: $1.5M.
Mobile Device Loss/Theft
25% of breachesCaregivers carry smartphones and tablets to client homes. Lost or stolen devices with unencrypted patient data are reportable breaches.
Insider Threats
15-20%Current or former employees who access patient data beyond their authorization. Includes snooping, data theft, and unauthorized disclosure.
Unsecured Networks
Common in fieldCaregivers connecting to client Wi-Fi networks or public hotspots without VPN protection. Data interception risks are high on open networks.
Vendor/Third-Party Breach
30% of breachesSoftware vendors, billing services, or cloud providers with access to patient data getting breached. Business Associate Agreements (BAAs) are critical.
HIPAA Security Rule: The Three Safeguards
The HIPAA Security Rule requires three categories of safeguards for electronic protected health information (ePHI). Every home care agency must implement all three for full HIPAA data security compliance.
Administrative Safeguards
9 standards, the majority of HIPAA Security Rule
- Security Management Process (risk analysis, risk management)
- Assigned Security Responsibility (designated HIPAA Security Officer)
- Workforce Security (authorization, supervision, clearance procedures)
- Information Access Management (access authorization, establishment, modification)
- Security Awareness Training (security reminders, malware protection, login monitoring, password management)
- Security Incident Procedures (response and reporting)
- Contingency Plan (data backup, disaster recovery, emergency mode operations)
- Evaluation (periodic technical and nontechnical evaluation)
- Business Associate Contracts (BAAs with all vendors accessing ePHI)
Physical Safeguards
4 standards covering physical access
- Facility Access Controls (contingency operations, facility security plan, access control, maintenance records)
- Workstation Use (policies for workstation functions and physical attributes)
- Workstation Security (physical safeguards restricting access)
- Device and Media Controls (disposal, media reuse, accountability, data backup and storage)
Technical Safeguards
5 standards covering technology controls
- Access Control (unique user identification, emergency access, automatic logoff, encryption and decryption)
- Audit Controls (hardware, software, and procedural mechanisms to record and examine activity)
- Integrity Controls (mechanisms to authenticate ePHI, protect from alteration or destruction)
- Person or Entity Authentication (verify identity of persons seeking access to ePHI)
- Transmission Security (integrity controls and encryption for ePHI transmitted over networks)
Security Risk Assessment
Answer 10 questions to assess your home care agency's data security posture. Receive a risk score and identify critical vulnerabilities in your home care cybersecurity practices.
1.Do all users have unique login credentials (no shared passwords)?
2.Is patient data encrypted at rest and in transit?
3.How are caregiver mobile devices secured?
4.Do all staff complete annual HIPAA security awareness training?
5.Have you completed a HIPAA Security Risk Assessment in the past 12 months?
6.Do you have a written incident response plan for data breaches?
7.Do all vendors with patient data access have signed BAAs?
8.What is your password policy?
9.How is patient data backed up?
10.Are paper records and physical devices with ePHI secured?
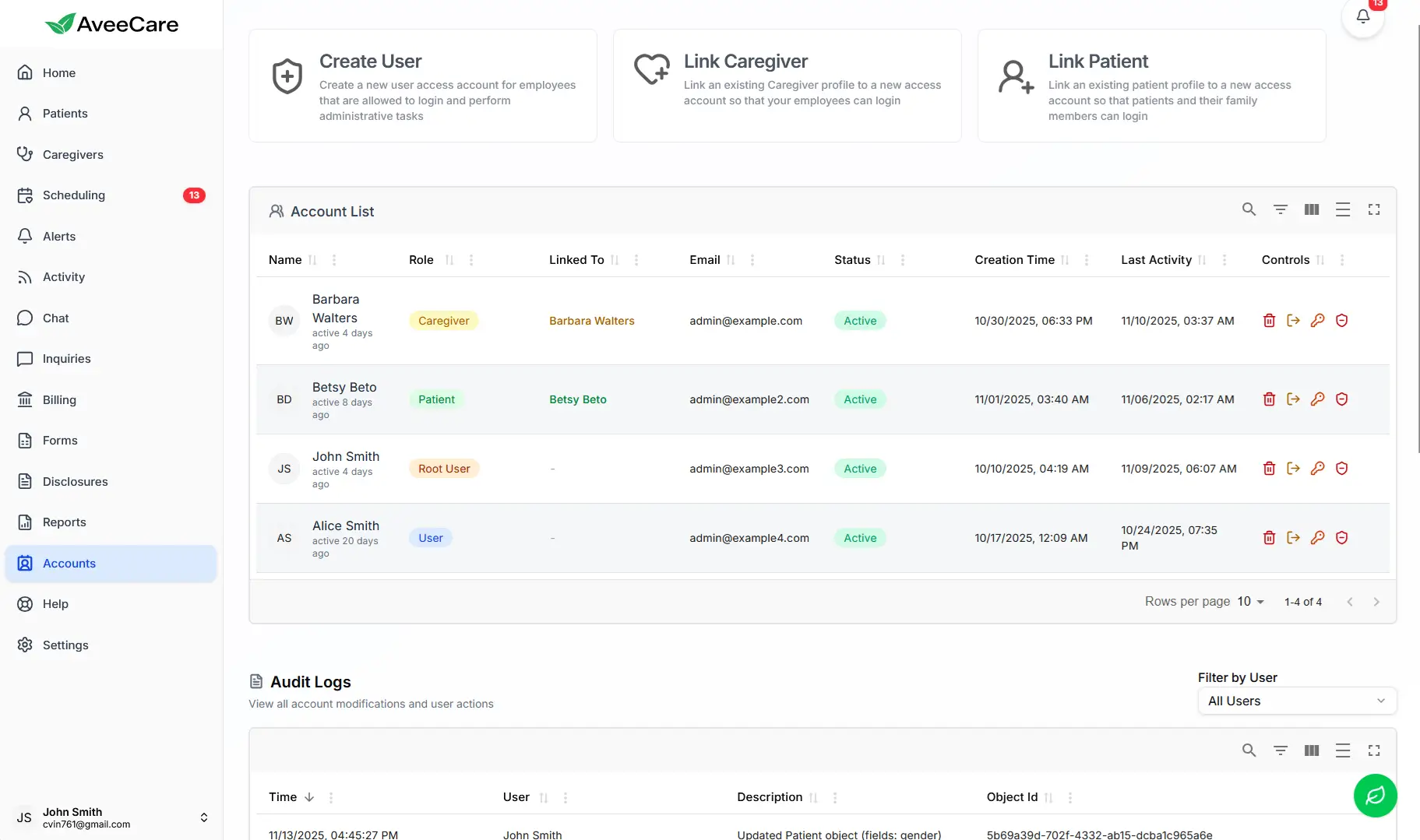
Role-Based Access Controls
Manage who can access patient data with granular permission settings
Data Breach Response Checklist
If a breach occurs, follow this step-by-step checklist based on HIPAA Breach Notification Rule requirements. Click each step to mark it complete as you work through your response.
Contain the Breach
Immediately- Isolate affected systems and devices
- Change compromised passwords and access credentials
- Disable unauthorized access points
- Preserve evidence (do not delete logs)
Investigate & Document
Within 24-72 hours- Identify what data was accessed or exfiltrated
- Determine how many individuals are affected
- Document the timeline of the breach
- Engage forensics experts if needed
- Identify the root cause and attack vector
Notify Affected Individuals
Within 60 days of discovery- Send written notification to all affected individuals
- Include description of what happened and what data was involved
- Provide steps individuals can take to protect themselves
- Offer identity theft protection if SSNs or financial data exposed
Notify HHS
Within 60 days (or annually if under 500)- Submit breach report through HHS breach reporting portal
- If 500+ individuals affected, notify within 60 days
- If under 500, may report annually (within 60 days of calendar year end)
- Provide detailed information about the breach and remediation
Notify Media (if 500+ affected)
Within 60 days- Issue press release to prominent media outlets in affected states
- Provide toll-free number for affected individuals
- Prepare public statement and FAQ
Remediate & Prevent
Ongoing- Implement corrective actions to prevent recurrence
- Update security policies and procedures
- Conduct additional staff training
- Document all remediation steps for compliance records
- Review and update incident response plan based on lessons learned
Security Policy Template Builder
Select the security policies your agency needs and view the key elements each policy should contain. Use this as a framework for creating or updating your written policies.
Select the security policies you need to create or update. Each policy includes key elements that should be addressed.
Access Control Policy
Mobile Device Policy
Data Handling Policy
Incident Response Policy
Frequently Asked Questions
Data Sources
HHS Office for Civil Rights
HIPAA Security Rule guidance, breach notification requirements, enforcement actions, and annual breach report data.
National Institute of Standards and Technology
Cybersecurity Framework (CSF), Special Publication 800-66 (HIPAA guidance), and encryption standards.
Office of the National Coordinator for Health IT
Health IT security resources, interoperability standards, and health information exchange security guidelines.
FBI Internet Crime Complaint Center
Healthcare sector threat reports, ransomware trends, and cybercrime statistics for healthcare organizations.
HIPAA-Compliant Software from Day One
AveeCare is built on AWS with enterprise-grade security. Role-based access controls, encrypted data at rest and in transit, audit logging, and automatic session management are built into every account. No security configuration required on your end.
- HIPAA-compliant cloud infrastructure on AWS with SOC 2 compliance
- Role-based access controls with granular permission management
- AES-256 encryption at rest and TLS 1.3 encryption in transit
- Automatic session timeout and audit logging for all ePHI access
- Secure HIPAA-compliant messaging replacing unsecured texting
Sources & Disclaimer
Statistics and requirements in this guide are compiled from HHS OCR, NIST, ONC, and FBI IC3 publications. HIPAA requirements are summarized for educational purposes. Security threats and statistics reflect data available through Q1 2026.
This guide is for educational purposes and does not constitute legal or compliance advice. HIPAA requirements are complex and fact-specific. Consult qualified legal counsel and certified security professionals for your agency's specific compliance needs. The risk assessment tool is educational and does not replace a formal HIPAA Security Risk Assessment.
Last updated: April 2026. AveeCare reviews and updates resource guides annually.